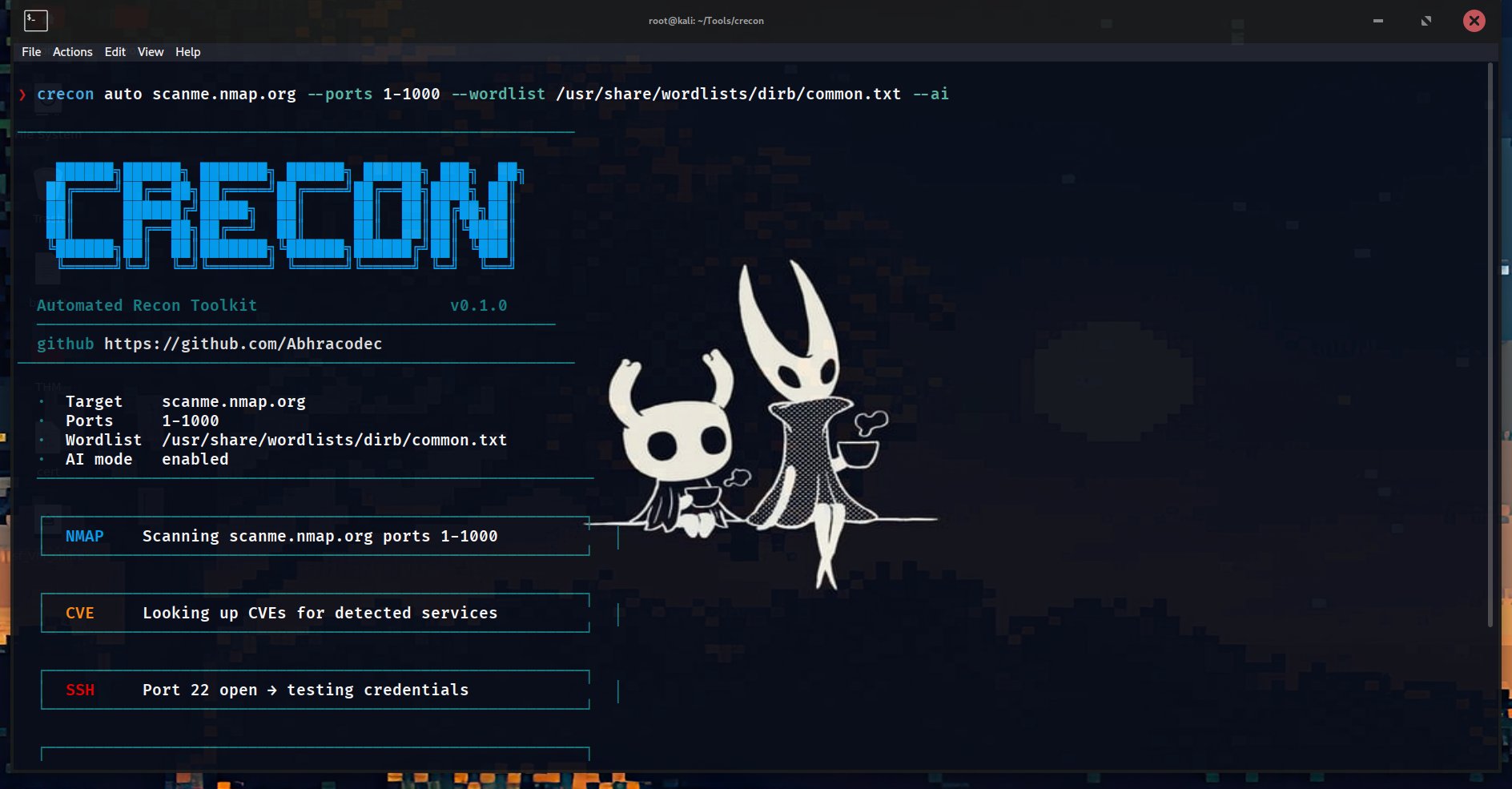
⚡ One command. Full recon. Nmap → CVE lookup → SSH testing → directory brute-force → web crawl → Nuclei → AI-generated attack paths with exact payloads. Zero manual chaining.
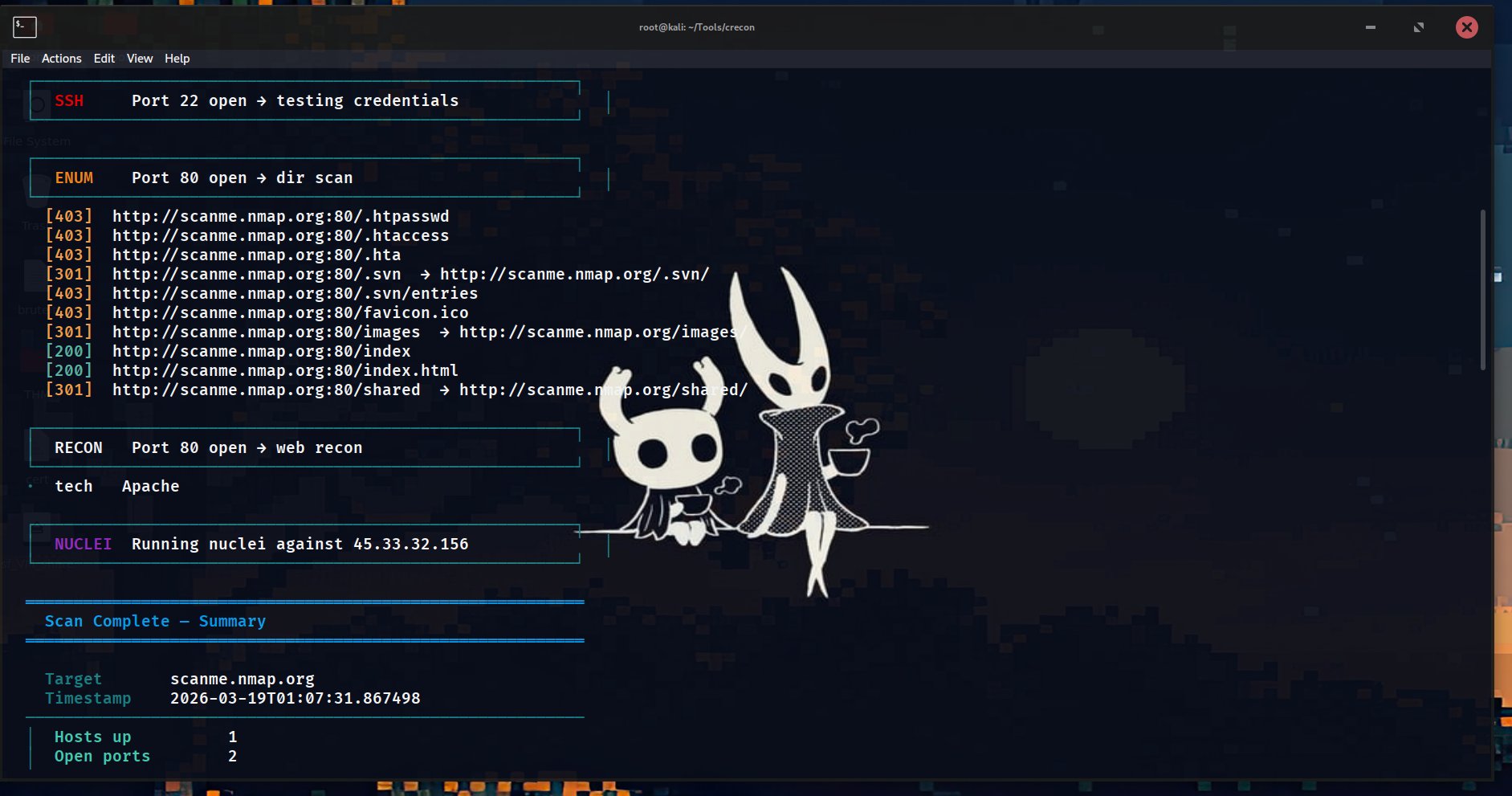
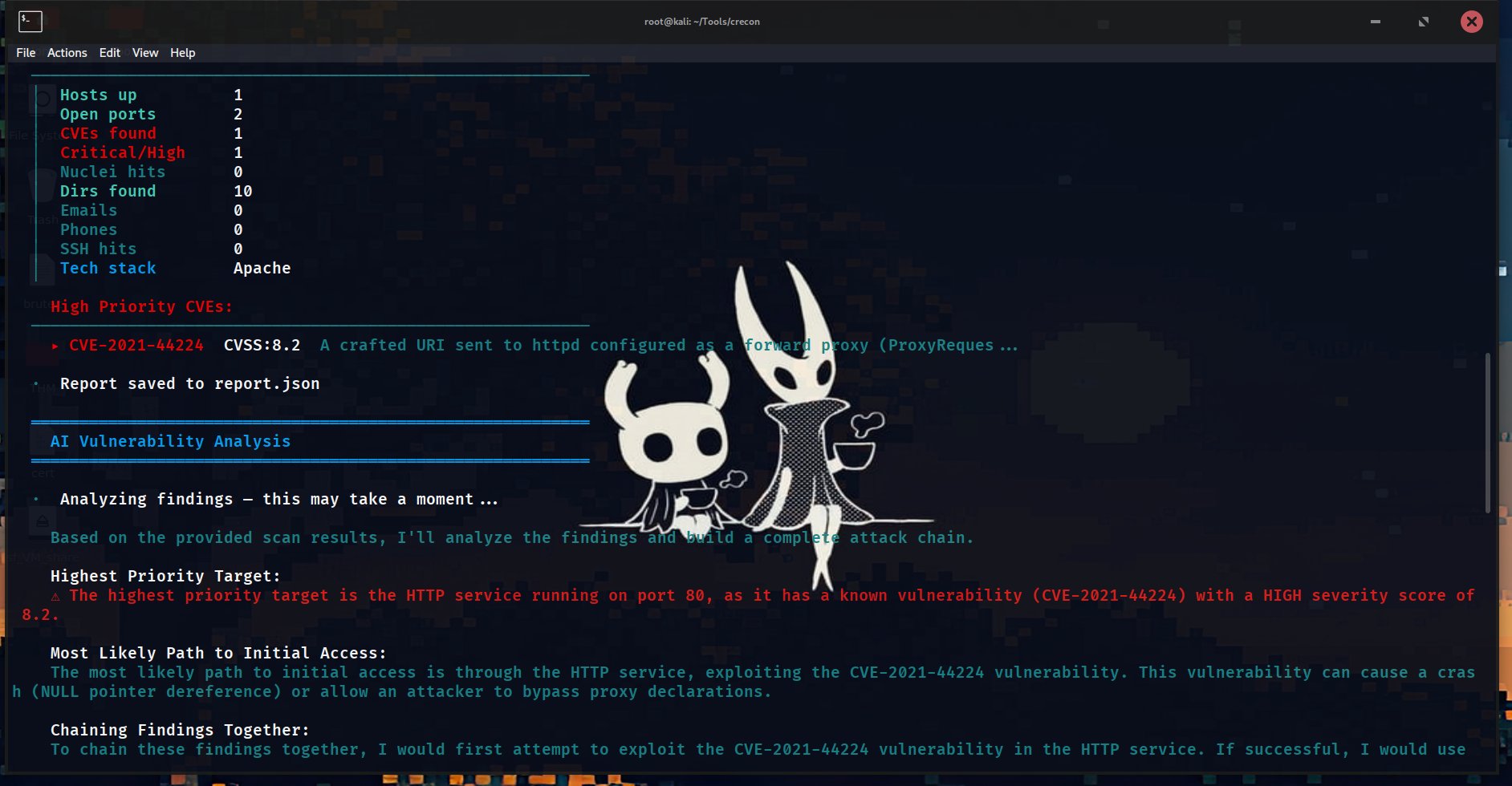
Automates the first phase of every engagement. Port 80 open → triggers directory brute-force, web crawl, Nuclei CVE validation automatically. Port 22 open → auto-tests default SSH credentials. NVD CVE lookup fires on every detected service version. All findings are piped to an AI layer that generates actual attack paths — not generic advice, but exact commands and payloads.
Supports 5 AI providers (DeepSeek-R1, Groq, Gemini, OpenAI, Anthropic) with automatic fallback. Installable as a native Kali Linux command. Built for real engagements, not demos.
PythonNmapNuclei
paramikoBeautifulSoupdnspython
NVD APIDeepSeek-R1subprocess
ThreadPoolExecutorsocket
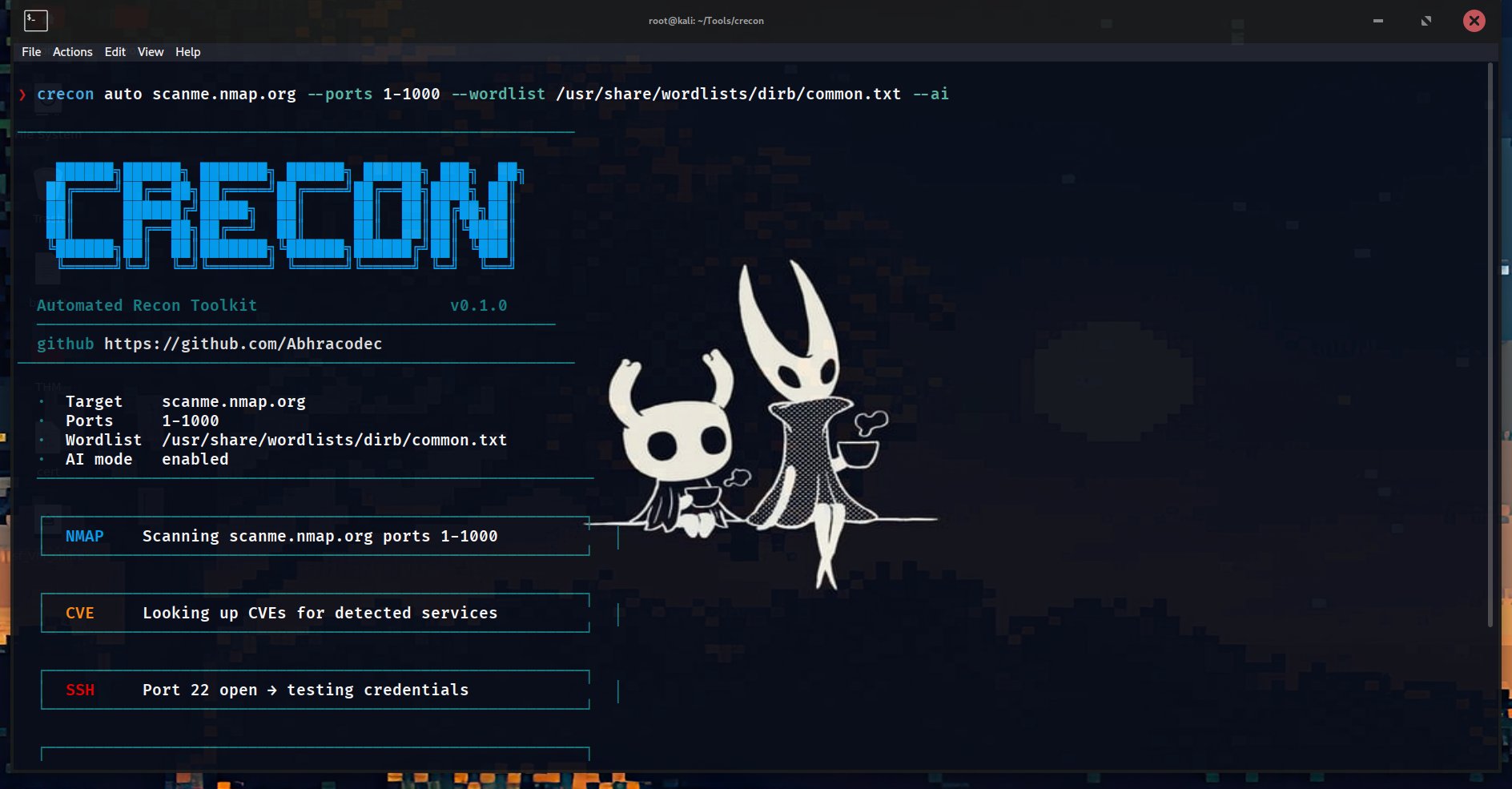
auto mode — full chain: Nmap → CVE lookup → SSH test → dir enum → web recon → Nuclei
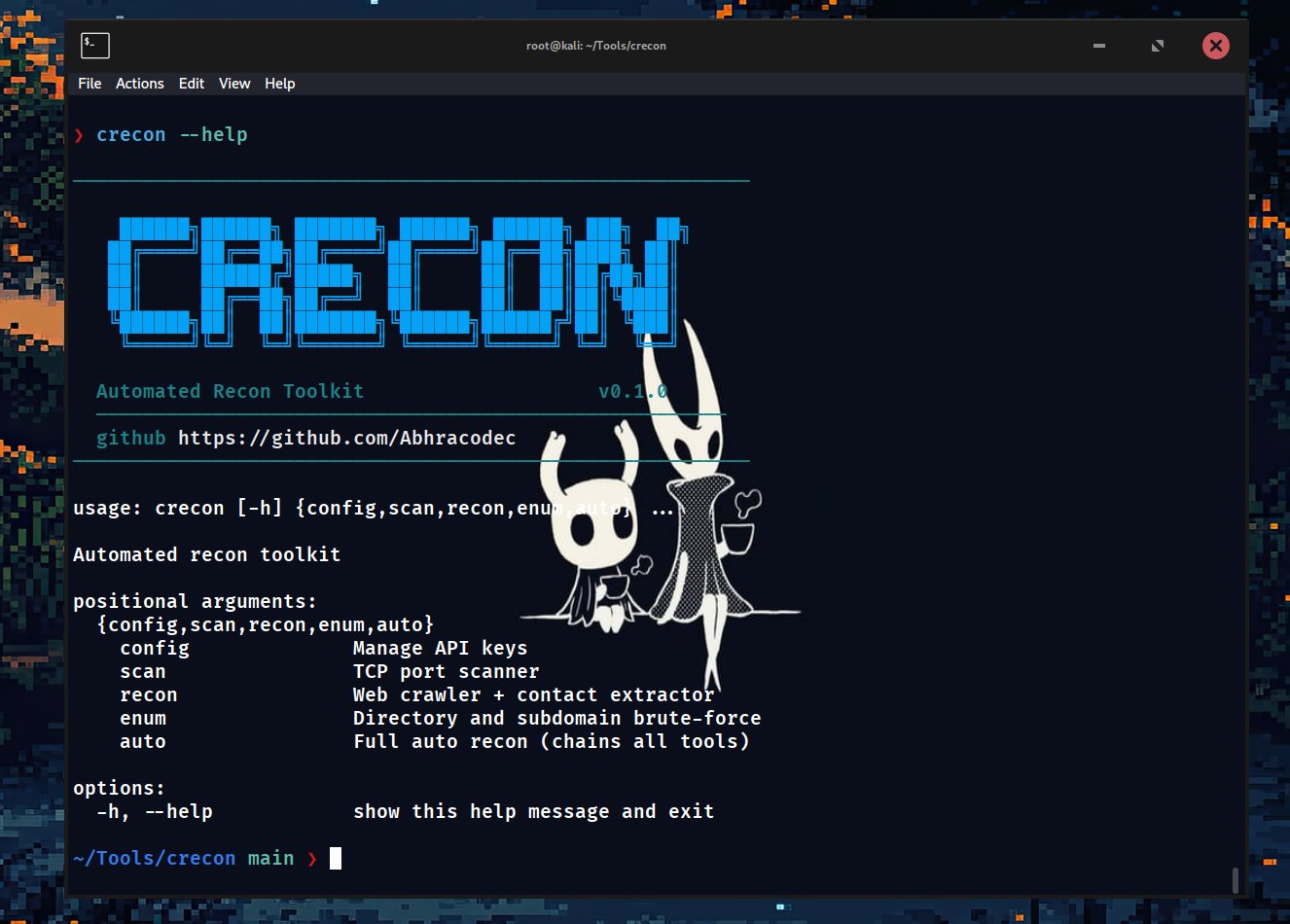
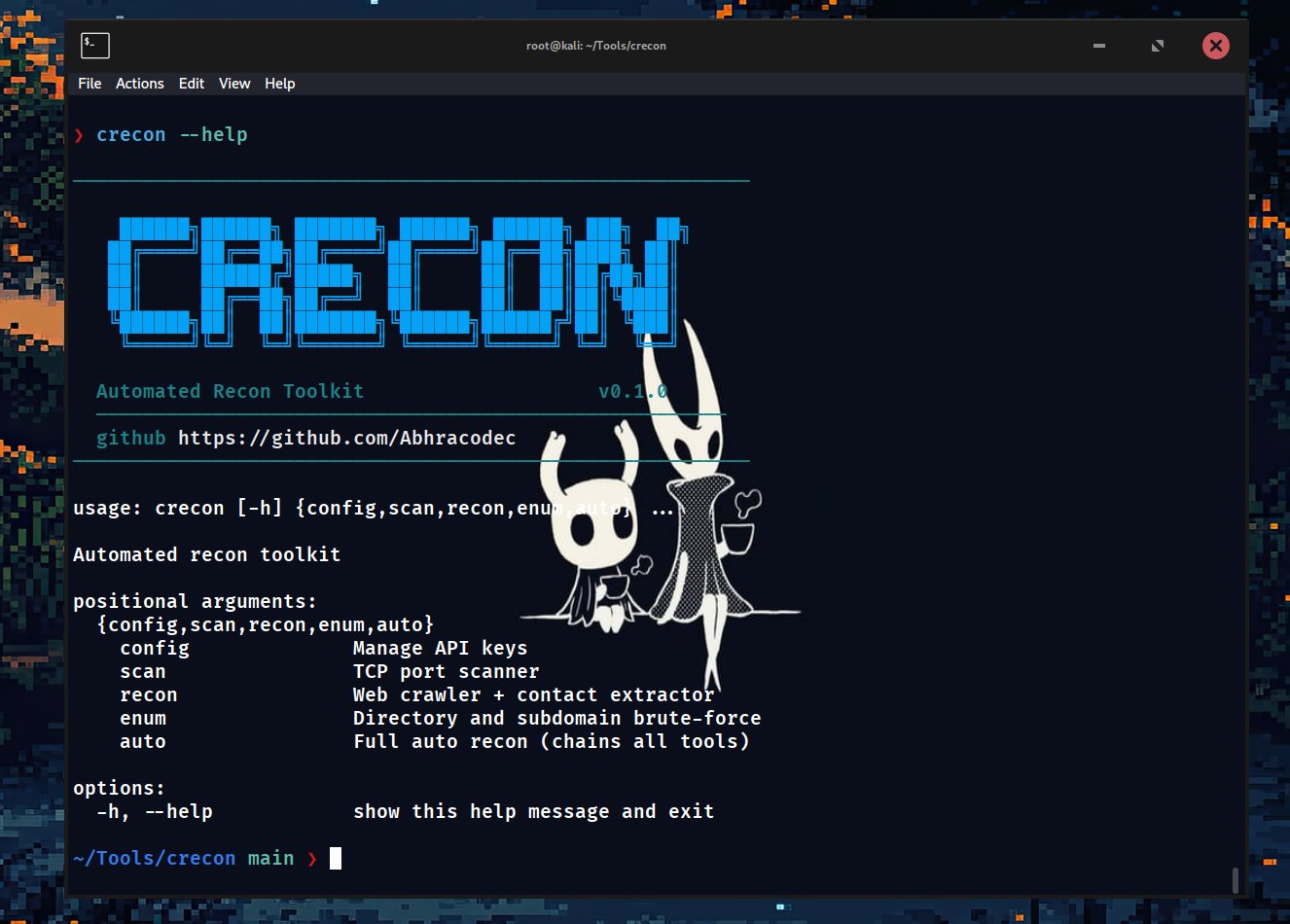
crecon --help — banner + subcommands
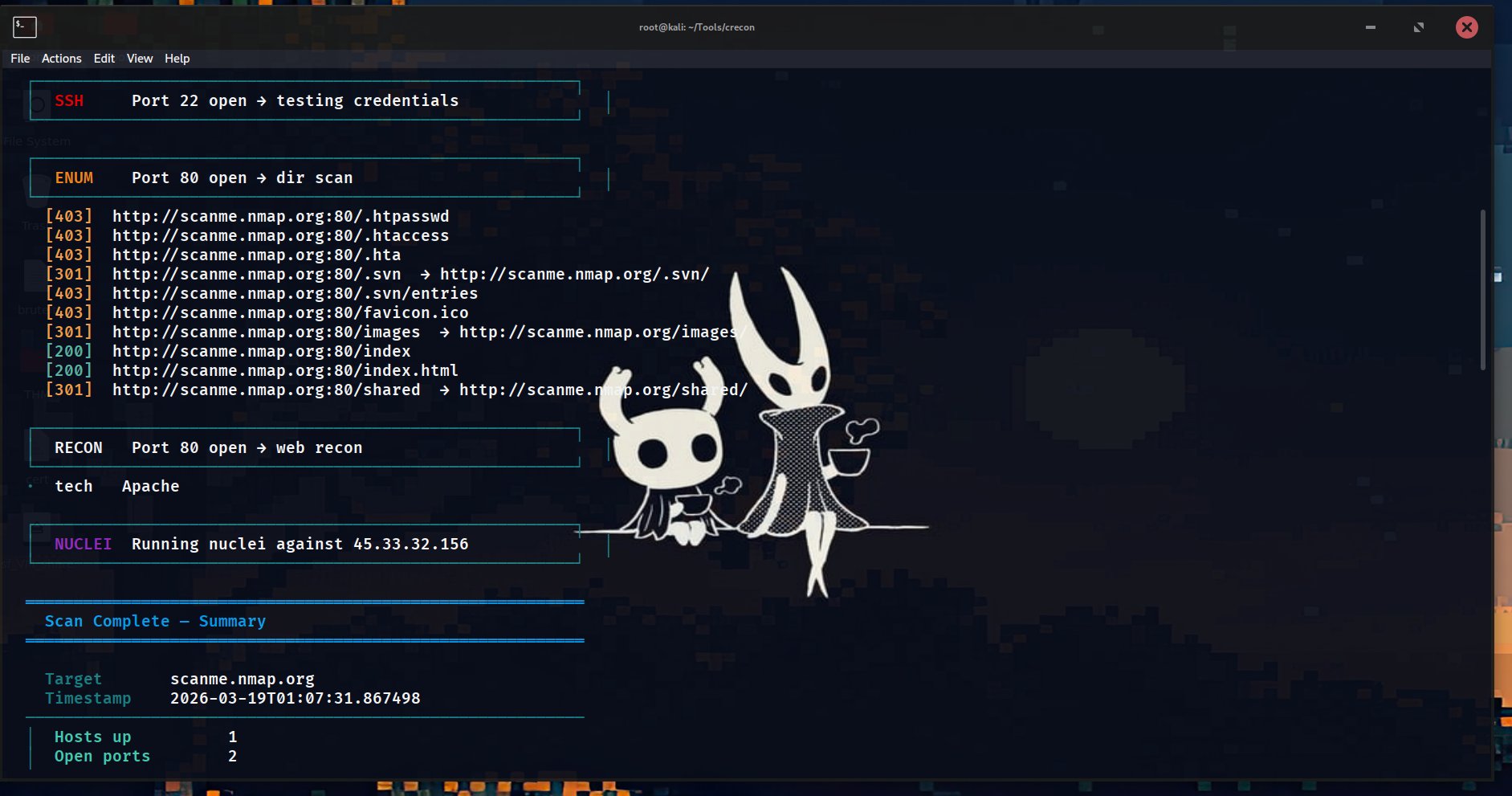
dir enum + recon — .htpasswd, .svn, Apache detected
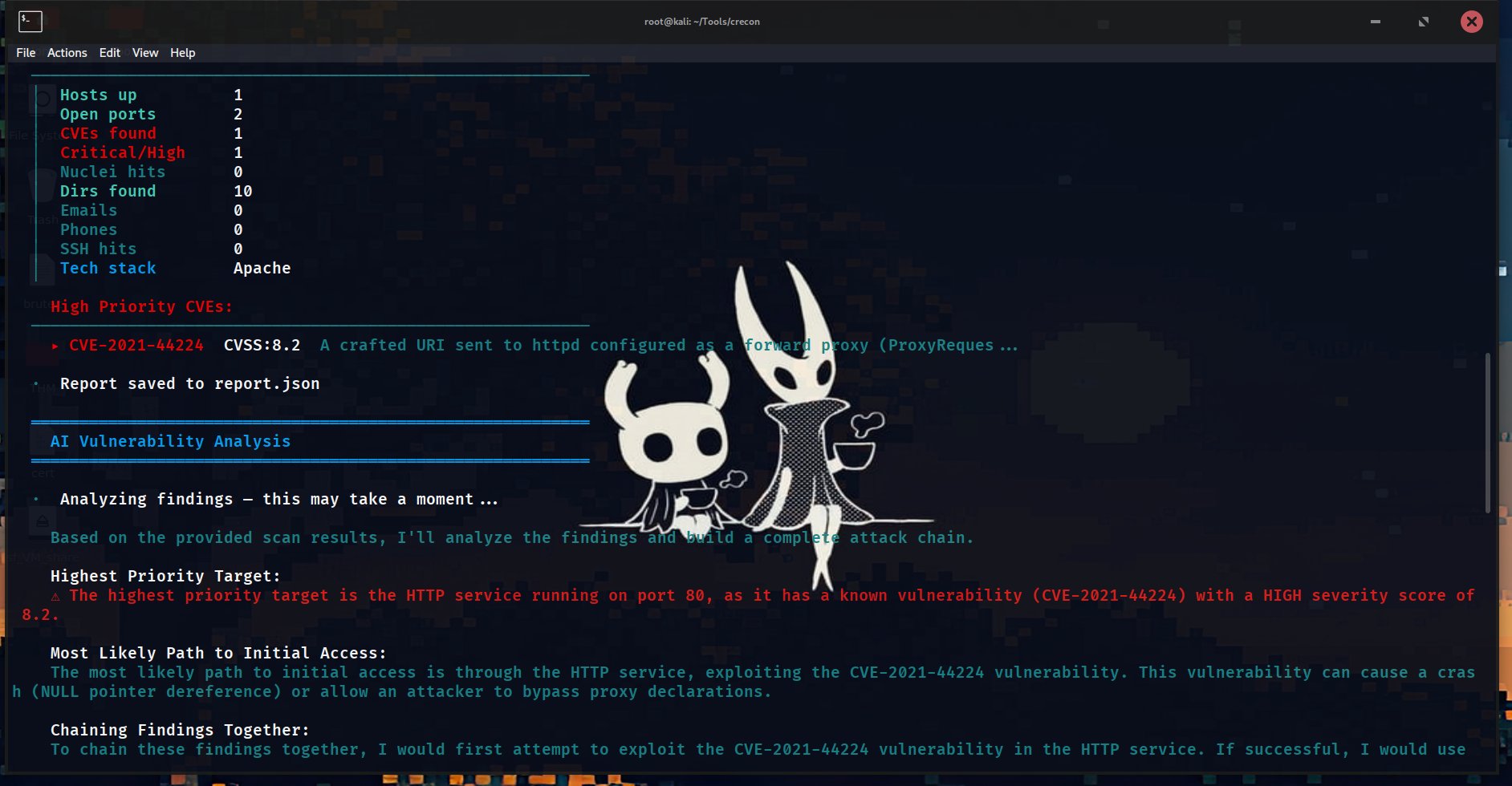
AI analysis — CVE-2021-44224 (CVSS 8.2) — complete attack chain with exact commands